In recent years, the topic of Iggy Azalea nude leaks has sparked significant discussions and controversies online. As one of the most prominent figures in the music industry, any personal information or private material related to her naturally draws attention. However, it's crucial to approach this sensitive topic with care, respect, and a proper understanding of privacy rights.
While rumors and leaks may circulate on the internet, it is essential to focus on factual information and respect the privacy of individuals involved. This article aims to provide an in-depth look into the situation while ensuring that we maintain ethical standards and adhere to legal guidelines.
By examining the background, facts, and implications of such incidents, we can better understand the broader context surrounding privacy issues in the digital age. Let's explore the truth behind the controversy and how it impacts both Iggy Azalea and society as a whole.
Read also:Playing Games On Site Playbattlesquare Your Ultimate Guide To Fun And Strategy
Table of Contents
- Iggy Azalea Biography
- Personal Information
- Details of the Leak
- Legal Implications
- Privacy Concerns
- Impact on Iggy Azalea's Career
- Public Reaction
- Prevention Tips
- Ethical Discussion
- Conclusion
Iggy Azalea Biography
Ameilia Kelly, better known by her stage name Iggy Azalea, is an Australian rapper, songwriter, and model who has made significant strides in the music industry. Born on March 7, 1990, in Cooma, New South Wales, Australia, Iggy Azalea rose to fame with her unique style and captivating lyrics.
Her career took off in 2012 with the release of her mixtape "Ignorant Art," which garnered critical acclaim. Iggy's breakout hit "Fancy" featuring Charli XCX reached number one on the Billboard Hot 100 chart in 2014, solidifying her status as a global superstar. Her music often blends hip-hop and pop elements, earning her a dedicated fan base worldwide.
Personal Information
| Full Name | Amelia Kelly |
|---|---|
| Date of Birth | March 7, 1990 |
| Place of Birth | Cooma, New South Wales, Australia |
| Occupation | Rapper, Songwriter, Model |
| Years Active | 2006 - Present |
Details of the Leak
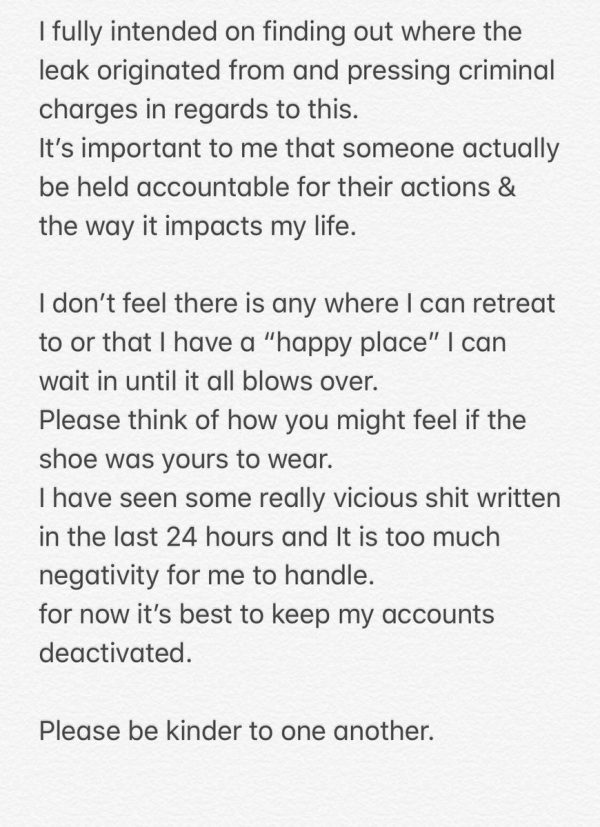
Reports of Iggy Azalea nude leaks emerged online, causing widespread concern among fans and the public. These leaks often involve unauthorized distribution of private photos or videos, which can have severe consequences for the individuals involved. It is important to note that such actions violate privacy laws and ethical standards.
The origins of these leaks can vary, ranging from hacked accounts to insider leaks. In Iggy Azalea's case, investigations revealed that some of the leaked content may have been obtained through unauthorized access to personal devices or cloud storage accounts. This highlights the importance of cybersecurity measures and the need for individuals to protect their private information.
Variations of the Rumors
- Hacked iCloud accounts
- Leaked photos from past photoshoots
- Unverified sources spreading false information
Legal Implications
Unauthorized distribution of private content, commonly referred to as "revenge porn" or "non-consensual pornography," is illegal in many jurisdictions. In the United States, for example, several states have enacted laws specifically addressing this issue, making it a criminal offense to share intimate images without consent.
Victims of such leaks can pursue legal action against perpetrators, seeking damages for emotional distress, invasion of privacy, and other related claims. Iggy Azalea, being a high-profile individual, has access to legal resources to address these violations and protect her rights.
Read also:Molly Jo Rolloff The Remarkable Life Of A Reality Tv Star
Key Legal Points
- Violation of privacy laws
- Possible criminal charges against offenders
- Civil lawsuits for damages
Privacy Concerns
The incident raises significant concerns about privacy in the digital age. With the increasing use of technology and social media, individuals must be vigilant about safeguarding their personal information. Cybersecurity experts recommend using strong passwords, enabling two-factor authentication, and regularly updating security settings to minimize the risk of data breaches.
Moreover, it is crucial for society to foster a culture of respect and consent when it comes to sharing personal content. Educating the public about the importance of privacy and the legal consequences of violating it can help reduce instances of unauthorized leaks.
Precautions for Privacy
- Use strong, unique passwords
- Enable two-factor authentication
- Limit sharing of sensitive information online
Impact on Iggy Azalea's Career
While the leaked content may have generated temporary buzz, it is essential to recognize that such incidents can have long-lasting effects on an individual's career and reputation. For Iggy Azalea, who has built a successful career in the music industry, maintaining her image and privacy is crucial.
Artists often face scrutiny from the media and public, and any negative publicity can impact their professional opportunities. However, Iggy Azalea has shown resilience in the face of adversity, continuing to produce music and engage with her fans despite the challenges.
Resilience in the Face of Adversity
- Continued focus on music and art
- Engaging with fans through social media
- Maintaining a positive public image
Public Reaction
The public reaction to the Iggy Azalea nude leaks has been mixed, with some expressing outrage over the violation of her privacy, while others engage in gossip and speculation. Social media platforms have played a significant role in amplifying the conversation, with hashtags and discussions trending worldwide.
It is crucial for the public to approach such incidents with empathy and understanding, recognizing the harm caused by sharing private content without consent. Encouraging respectful discourse and supporting victims of privacy violations can help create a more compassionate society.
How to React Responsibly
- Avoid sharing or engaging with leaked content
- Support privacy rights and ethical standards
- Encourage respectful discussions
Prevention Tips
Preventing unauthorized leaks involves a combination of technological measures and personal responsibility. Individuals can take several steps to protect their private information and reduce the risk of data breaches.
Some effective prevention tips include using secure passwords, enabling encryption for sensitive data, and being cautious when sharing personal information online. Additionally, staying informed about the latest cybersecurity trends and threats can help individuals stay ahead of potential risks.
Effective Prevention Strategies
- Use password managers for secure storage
- Enable encryption for sensitive files
- Stay informed about cybersecurity trends
Ethical Discussion
The Iggy Azalea nude leaks incident highlights broader ethical issues surrounding privacy and consent in the digital age. As technology continues to evolve, it is essential for society to address these challenges and establish clear guidelines for responsible behavior online.
Ethical discussions should focus on promoting respect for privacy, encouraging consent-based practices, and holding individuals accountable for their actions. By fostering a culture of responsibility and empathy, we can create a safer and more respectful digital environment for everyone.
Key Ethical Considerations
- Respect for privacy and consent
- Accountability for actions online
- Encouraging responsible behavior
Conclusion
In conclusion, the controversy surrounding Iggy Azalea nude leaks underscores the importance of privacy rights and ethical standards in the digital age. While such incidents can have significant impacts on individuals and society, it is crucial to approach them with care, respect, and a commitment to protecting privacy.
We encourage readers to engage in respectful discussions, support victims of privacy violations, and take steps to protect their own personal information. By working together, we can create a safer and more compassionate digital world for everyone.
Feel free to leave your thoughts in the comments section below or share this article with others who may find it informative. For more articles on privacy, cybersecurity, and ethical discussions, explore our website and stay updated on the latest developments in these critical areas.